Street Crime
In the UK in 2016, there were almost half a million mobile phones stolen, with 60,000 mobile thefts and robberies in London alone, most of them iPhones.
The UK government Home Office paper “Reducing Mobile Phone Theft and Improving Security” shows that victims are most likely to have their phones pick-pocketed or stolen when the device is briefly left unattended. The data also shows that certain groups are especially vulnerable: 14-24-year-olds, and particularly women in this age group, are more likely than any other group to be victims of mobile phone theft.
In the UK, the Sun newspaper reported that the demand for stolen devices was fuelling Britain’s recent epidemic of moped robbers. Some of these robberies have involved considerable violence with reports of thieves armed with axes, samurai swords, zombie knives and acid, snatching smartphones from pedestrians. According to London’s Metropolitan Police, in 2017 there was a threefold increase in crimes related to mopeds compared to the previous year.
Mobile Phone Theft Is on the Increase
Globally, smartphone theft is on the increase. In Peru, La Republica reported that 6,000 devices are stolen each day, while in Argentina, La Nacion reported that there are almost 5,000 thefts of mobile devices a day. The Colombian telecoms regulator CrC reported that mobile phone theft grew 79% in the first half of 2017 compared to the first half of 2016. And in Mexico, mobile theft is so prevalent that people are carrying dummy mobiles to hand over to thieves, instead of their real phones.
Street theft is only part of the issue. Criminal activity across warehousing, road freight and retail stores within the operator’s supply chain also result in large volumes of counterfeit or grey devices hitting the market. However, it’s street crime that makes the headlines due to its effect on the victims, and not least because of some of the violence involved.
Smartphones also carry so much personal information: banking details, email, photos, videos, music, apps, and private information. So, the consequences of having this information stolen can be profound. Lookout’s Phone Theft in America report found that:
- 10% of victims reported loss of company data
- 12% of victims had fraudulent charges made to their accounts
- 9% of victims had their identity stolen
It’s therefore unsurprising that the report found that a third of phone-theft victims would be willing to pay $1,000 to retrieve their stolen phone’s information. And 68% percent of phone theft victims stated that they’d be willing to put themselves in some degree of danger to retrieve a stolen device and the information on it.

Trafficking Stolen Devices – Black Market Phones
Often, after a phone is stolen, it is sold on to a middle man. A 2018 BBC documentary, Inside Britain’s Moped Crime Gangs, interviewed one such individual who buys stolen phones cheaply from the moped robbers and sells them on for twice the amount to Nigerian racketeers.
Stolen devices may also be shipped to eastern Europe first to be stripped of private information and to be reconditioned, before being moved on for sale in countries such as Nigeria, Algeria and India.
In the UK, the Sun newspaper discovered significant volumes of UK-used iPhones being sold for £560 in stores in Lagos, Nigeria. Stores advertised “UK phones and accessories” and “UK used phones at affordable prices”. The black market in stolen phones is booming due to soaring demand in a country where hi-tech gadgets are in short supply.
IMEI Global Database & GSMA Blacklist
Unlike countries in Europe, the US and South America, Nigeria has not signed up to the GSMA’s International Mobile Equipment Identity Database (IMEI Db) scheme which enables the blacklisting of stolen phones. Under this scheme, every phone is given a unique number (the IMEI) which is added to a global database. If the device is later reported stolen, it is blacklisted and rendered useless in countries that have signed up to the scheme. But, until Nigeria signs up, the black market will continue to thrive, and this in turn will fuel the crime wave in other nations.
This also explains why many stolen handsets are often traced to Nigeria, Southeast Asia and the Middle East, where smartphone prices can be up to ten times higher than in western markets because handsets are not subsidized by carriers in these markets.
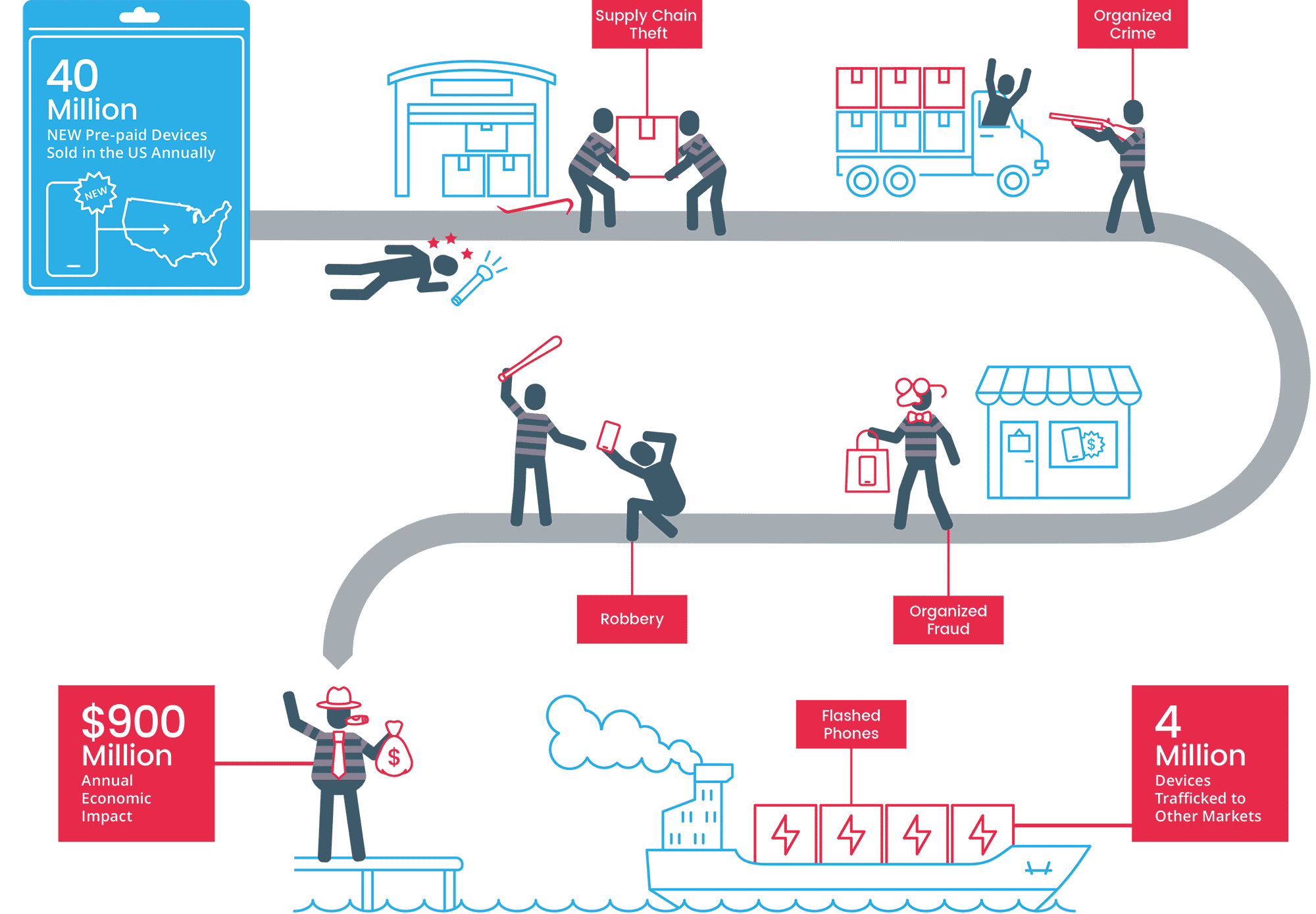
In the USA alone, GSMA estimates that more than four million prepaid devices are trafficked annually, with the cost of bulk prepaid trafficking totaling US$900m. That’s a staggering loss of US$225 per device trafficked. These figures are from the prepaid segment of the US alone. Aggregating figures globally, from both the postpaid and prepaid markets suggests a much larger figure. In fact, if these figures are extrapolated globally, we estimate that device-based fraud may have an annual impact on mobile operators of at least US$10bn per annum. This is likely a conservative figure, based on our mobile operator customers and prospects telling us that illegal activity affects between 5% and 30% of the devices that they sell.
Involvement of Organized Crime
Given the value of devices and the gains to be made, reports suggest that sophisticated, organized crime is behind some of the larger-scale theft. The cost to phone-theft victims is considerable, as is the cost to the industry, with OEMs, MNOs, MNVOs, distributors, supply chain players and retailers all bearing the impact.
There is such a massive global market for stolen smartphones, that one company in the US accepted so many stolen iPhones and iPads (to ship overseas) it needed an armored truck to deliver the cash used to pay for them all.
Organised crime gangs appear to be are involved at various levels:
- Trafficking stolen devices in bulk to eastern Europe to be stripped of private information and reconditioned.
- Shipping stolen devices in bulk for sale in countries, such as Nigeria, where device blacklisting is not used.
- Stealing from the supply chain. Devices are being stolen while in transit from the manufacturer to the warehouse to the retailer.
- Stealing from retail stores, sometimes by insiders from “back of house” where devices are being prepped for sale.
Cell Phone Theft Prevention – Tackling the problem
Current measures designed to tackle the epidemic of smartphone theft are clearly not working. In Farrell’s Preventing phone theft and robbery: the need for government action and international coordination report, he states:
“The banning of stolen handsets from networks has been around for 20 years, but remains little used internationally. Where used, its effectiveness is hindered by implementation problems, reprogramming, easy fencing opportunities, and international trafficking. Kill-switches where the user remotely disables a handset and deletes data have potential but, if non-permanent, are likely to experience similar limitations.”
However, there is a solution to combat device-related crime: Trustonic’s Asset Lifecycle Protection Service (ALPS).
Trustonic has developed a holistic solution to tackle the on-device security issues that operators and others in the mobile ecosystem face. The Telecoms Platform is a mobile device locking SaaS and the issues of sold but not activated (SBNA) and activated but not used (ABNU) device exploitation.
ALPS is integrated directly into the device manufacturing process, so protection is in place from the moment devices are built and operational throughout their lifecycle. ALPS secures the device at its very core – in the CPU and modem firmware – giving operators and mobile virtual network operators (MVNOs) a secure communication path to control the device’s modem to allow or restrict device communications.
Because ALPS prevents a stolen device from being unlocked, it effectively renders the device worthless thus removing the incentive to steal it. Nor can a locked device be used on another network, so even if a stolen device is shipped to another country that doesn’t subscribe to the GSMA’s blacklist, it cannot be activated on the network.
By implementing ALPS, operators can turn the tide on crime. That’s why ALPS is trusted by some of the largest operators and has been implemented on tens of millions of devices.
For more information about the solution visit – https://www.trustonic.com/device-locking/
Sources
https://transition.fcc.gov/cgb/events/Lookout-phone-theft-in-america.pdf
https://www.theverge.com/2013/7/15/4524172/us-smartphone-trafficking-black-market
https://www.thesun.co.uk/news/5957717/nigeria-black-market-fuels-britain-moped-theft/
https://www.gov.uk/government/news/mobile-phone-theft-paper-highlights-models-targeted-by-thieves
https://imeidb.gsma.com/imei/index#
https://blog.lookout.com/phone-theft-in-america
https://crimesciencejournal.biomedcentral.com/track/pdf/10.1186/s40163-014-0015-0
https://www.lanacion.com.ar/tecnologia/por-dia-se-roban-5000-celulares-en-la-argentina-nid1921944