A best practice security principle is one of separation. If the ‘bad guys’ are outside a barrier and your assets are inside, then you are halfway there. This is the principle behind a network firewall, or process separation in an operating system. Whilst good in principle, if you are relying on separation provided by a huge, complex system – for example, Android – it is hard to imagine that this separation alone is going to be enough.
I was amazed when I first discovered my mobile phone, and almost every mobile phone for that matter, does not only run Android but also a second, secure, operating system, isolated from Android by hardware mechanisms baked into the CPU. This operating system is used at arms-length for features like biometric unlock, DRM and ‘disk’ encryption. But, wouldn’t it make sense to run our finance and other sensitive applications there as well? That way they could be safe from prying eyes and malware.
It turns out that we can do just that. Trustonic is a long-time purveyor of such secure operating systems, or Trusted Execution Environments (TEEs) as they are known. More importantly, we are part of standards body, GlobalPlatform, tasked with ensuring that TEE vendors all provide a similar level of security and consistent APIs for developers. Huawei is also a member of the body, and its TEE, iTrustee, is present on almost every Huawei phone, alongside Android.
In fact, Huawei has just released a cool new phone, the P40. For the first time it has enabled access for third party developers to use its TEE. This was made possible through Huwaei’s partnership with Trustonic, which brings Huawei into the Trustonic Application Protection (TAP) ecosystem. Anyone who develops applications using the newly released TAP 2.0 SDK can now leverage the hardware security provided by iTrustee on Huawei devices, or by Trustonic’s TEE (Kinibi) on devices from other OEMs.
So, does this all mean better security? Absolutely, it enables more than that. TAP offers a broad SDK with many security focused features, such as broad crypto libraries, secure storage, and device and app attestation. One of the technologies Trustonic and Huawei have enabled is worth citing here – the Trusted User Interface (TUI). This enables the TEE OS to take complete control of the display and touch screen. ‘Take over’ here means these hardware devices literally disappear from the hardware bus used by Android. Instead they are remapped by the TrustZone™ capabilities in the ARM CPU so that that they are only visible to the TEE OS. Drivers in the TEE OS can now connect the screen to your app, and you get full and completely unfettered access to the UI. Malware is literally locked on the wrong side of a big, fat hardware firewall.
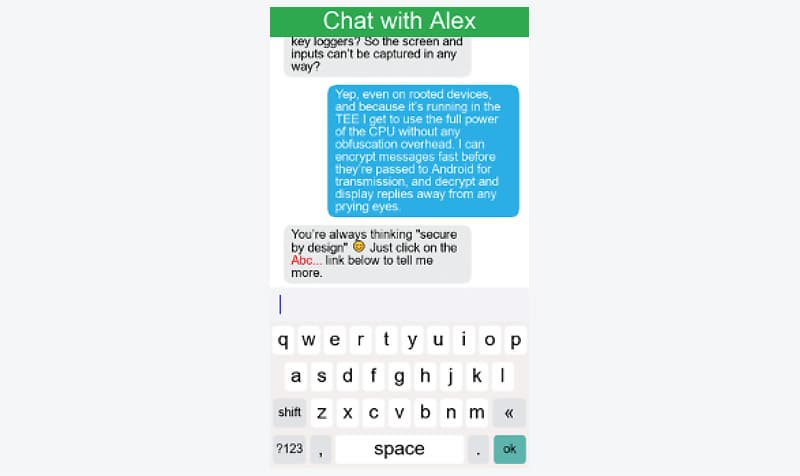
That means no keyloggers. No screen recording, or accessibility attacks on these protected screens. Rooting Android will not help – because the screen isn’t even in Android anymore. That gives the sort of level of security that can enable some exciting new use cases.
Companies like Volkswagen want to use this to share car keys securely, and others, such as Rubean are working on Mobile POS solutions, which can meet stringent PCI requirements. This can enable a whole new meaning for ‘end to end’ social message encryption, where each ‘end’ is a concrete bunker not a far-to-hackable Android app. The much misunderstood ‘attestation’ capabilities mean that your servers confidently recognise that it is your application binary, running in a hardware secure OS that is calling your APIs. There is no impersonating an attested TEE.
Our TUIs are not simply one-size-fits-all. They are fully programmable and brandable. Below is demo screenshot (TUI is so secure, screenshots on a real device are not possible). This screen capture from our TUI emulator shows secure input and output in a rich UI.
No security system is perfect. Running everything in the TEE wouldn’t solve all potential security issues. As a hardened security OS, the TEE isn’t as developer friendly as Android. Instead TAP applies that all-important principle of separation. Most of the app remains in Android, developed with according to the developer’s preference. However, the security critical part – the login, the payment, and the transaction signing, for example is is written as a set of trustworthy subroutines – or ‘Trusted App’ to use the TEE parlance. TUI screens themselves can be designed in XML but are translated at build time to secure code and all assets, down to every image and font glyph, have full integrity protection against any sort of Android malware attack.
At run time that trusted app is sent to run in the TEE, and if you are unlucky enough to be running on a device with no accessible TEE (such as one made by our friends in Cupertino), then it runs in the provided software TEE, protected using tools such as whitebox cryptography and code obfuscation.
Splitting your app in this way can cause time hurdles but it is a small cost for a big reward. It enables that all important separation between security critical code, where you should take special care and do everything possible to keep the ‘bad guys’ out, and general purpose code, where slick UX or rapid development may be more important. This separation also makes it easier to pass any external PEN test or certification review. These are both common needs of our customers.
Thanks to TAP, finance, crypto currency, car key and other critical apps can be made extremely secure. With our new partnership with Huawei, Trustonic has added the second biggest global Android OEM to the it ranks. Today’s announcement focuses on the P40 but as new devices are launched, and existing Huawei devices are upgraded to EMUI 10.1, TAP will rapidly grow to a significant part of the Android population. This is great news for anyone who develops, or uses, Android.
Richard Hayton
Chief Strategy and Innovation Officer, Trustonic
Request for early access
If you would like more information on how to start developing services for Huawei devices via Trustonic App Protection, please get in touch.

